Stop diffing router configs in Notepad++
IronDiff automatically pulls your configs, detects drift, and pushes a visual red/green diff to your team. Securely pull configs using a lightweight, local Docker agent—no inbound firewall rules required.
🔒 Device credentials never leave your local network. The agent only transmits encrypted diffs.
From Zero to Your First Diff in Under 5 Minutes
Deploying IronDiff is simple, secure, and requires zero inbound firewall rules.
Prep your local environment
Create a dedicated folder to securely store your persistent data and configurations locally.
mkdir irondiff && cd irondiffDeploy the lightweight agent
Run the container without opening any inbound firewall ports. This pulls configurations locally and pushes them outbound to the IronDiff cloud.
docker run -d \
--name irondiff \
--restart unless-stopped \
-p 5000:5000 \
-v $(pwd)/config:/app/config \
-v $(pwd)/data:/app/data \
-e TZ=America/Denver \
-e LICENSE_KEY=your-license-key-here \
irondiff/irondiff --daemonConfigure your devices
Navigate to https://localhost:5000 in your browser, log in securely, and add your target network hardware. IronDiff supports Cisco, Aruba, pfSense, Fortigate, and more.
Detect drift immediately
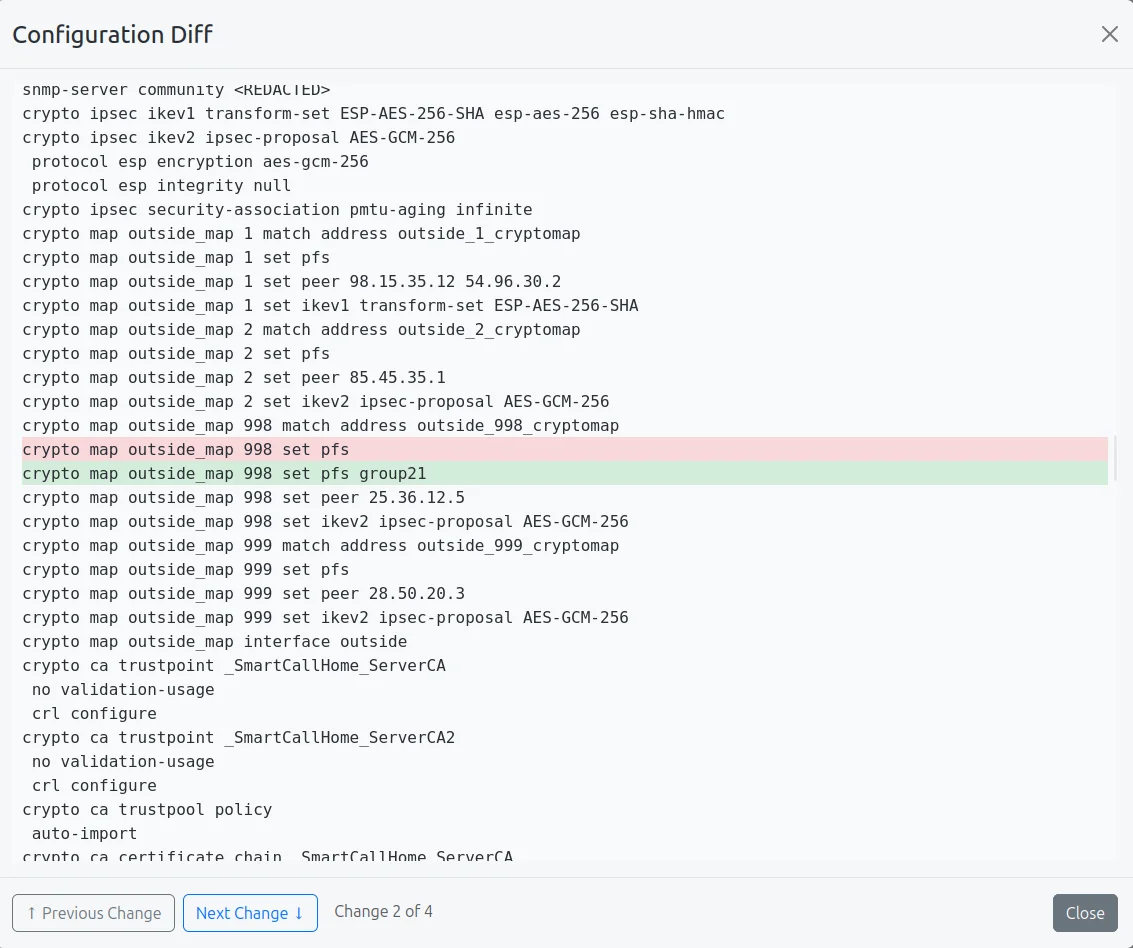
Hit the "Run Now" button to instantly pull your first configuration into the portal, or configure your automated polling schedule to track changes as they happen.
Free forever for up to 5 devices. No credit card required.

"IronDiff has completely automated our backup process. The peace of mind knowing our configurations are secure and versioned is invaluable."

"The diffing tool is a lifesaver. We can quickly identify what changed and when, which makes troubleshooting network issues so much faster."
How IronDiff Works
Connect
Zero Inbound Firewall Rules. Pull configurations locally and push them outbound using our lightweight on-prem agent.
Redact
Sensitive data like passwords are stripped in memory before storage.
Backup
Backups are optimized and stored securely with multi-layered protection and historical archiving.